
Checkmk importer
Versio.io can import, historize and process monitoring data from Checkmk.
Configuration
You can find the configuration option in Versio.io at Environment settings > OneImporter > Configurations > Checkmk.
Here you can edit all existing configurations, create new configurations or delete existing configurations.
To add a new configuration enter a Name for your importer and an Entity suffix (default: -check-mk) to clearly identify your Checkmk entities.
Note that the Entity suffix is fixed and cannot be changed afterwards.
Click Add to proceed to the configuration.
To edit an existing configurations click the arrow on the left of your importer name to expand the configuration options.
Following configuration options are available:
| Field | Description | Advice |
|---|---|---|
| Name | Meaningful name | Add the word "Checkmk" to identify importer when viewing the logs |
| Active | Option to activate and deactivate the configuration. Data is only imported if the configuration is activated. | |
| Server URL | Checkmk server URL to get data from | |
| Version | Select relevant Checkmk version | |
| Username | User name for Checkmk access | |
| Secret | Password for Checkmk access | See paragraph below for secret generation in Checkmk |
| Entities | Select all required entities | |
| Executing OneImporter | Select a Versio.io OneImporter to import the data based on the importer configuration. | Requires installed OneImporter: Installation instruction |
| Schedule time (cron format) | Determine the frequency of imports in CRON format | Learn more about CRON format: https://en.wikipedia.org/wiki/Cron |
Table: Checkmk configuration parameters
The following image is an example of a Checkmk configuration:
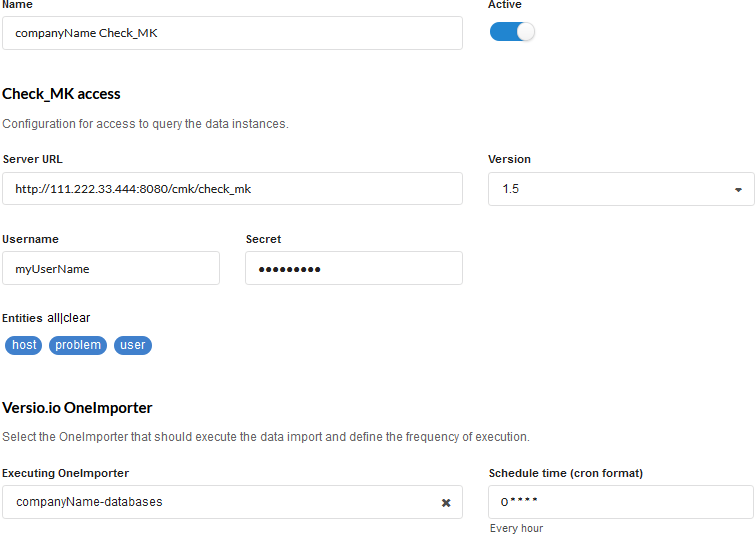 Figure: Example of a Versio.io Checkmk configuration
Figure: Example of a Versio.io Checkmk configuration
Install hardware & software inventory plugin
We strongly recommend activating the Hardware & Software Inventory Plugin in Checkmk. This will allow you to collect significantly more data about your infrastructure. Proceed as follows:
- Download plugin in Checkmk server user interface
- Save file at
<host>/../usr/lib/Checkmk_agent/plugins/for each Checkmk agent.
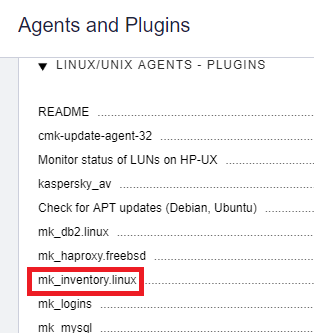
Figure: Agent plugin overview in Checkmk
See Checkmk manual for more information: https://docs.checkmk.com/latest/en/inventory.html
Secret generation
A user with an automation secret (similar to a token) for the Hetzner Cloud integration is required to access the Checkmk API.
Checkmk offers the concept of the automation user. These users are intended exclusively for remote control and do not permit normal GUI logins. Authorisation is achieved using specific variables in the URL.
An automation user is created like a normal user, but receives an automation secret instead of a password. This can be defined manually or can be generated automatically with the randomising die.
Just like a normal user, an automation user has a role and can also be a contact. With these you can thus restrict its permissions and visibility of hosts and services as required.
When opening websites automatically, you enter the following additional variables in the URL:
- _username the automation user's ID
- _secret the user's Automation secret
Example
The Versio.io OneImporter imports Checkmk data based on a specific configuration into entities with a suffix defined by you (default: -check-mk). To view the imported instances in Versio.io, select 'Asset & Configuration Repository → Instance Viewer'. There you can select your specific instance and click it for a detailed view in the instance history viewer.
The following image is an example of imported Checkmk data:
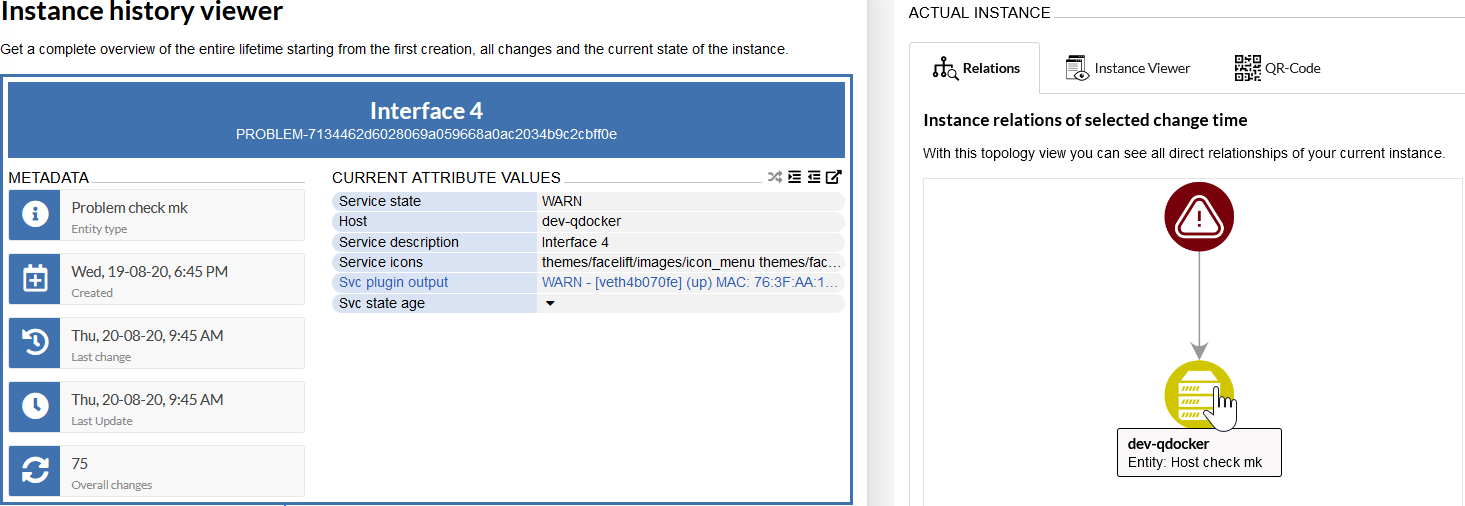
Figure: Overview of Versio.io Checkmk instance (left) and topology of related instances (right)